Never underestimate the power of a common enemy as a source of unity. On Friday Apple and Google, usually known for their commitment to outshining the other, announced a joint effort to help combat the spread of COVID-19. In it they propose to “develop opt-in contact tracing technology” to help contain the spread of the virus.
This announcement is exciting for two reasons. First, as we remain under house arrest over the Easter long weekend, anything that bolsters our chances of soon recommencing in-person visits with friends, wandering in public spaces and watching live sports is keenly welcomed. Second, the design of the program appears to have been done with the preservation of privacy in mind.
Nonetheless, our optimism should remain bridled as several details remain unknown and, in an AI age, we should be wary of anything that promises to track where we go and with whom we meet.
But first, what has been proposed and how is it meant to work?
The Gist of the Tech
According to their announcement, Apple and Google will collaborate to build a platform to alert you if someone you have recently encountered has since tested positive for COVID-19. The platform will employ Bluetooth technology to exchange signals with nearby phones approximately every five minutes and store a record of these transmissions. If someone with a smartphone tests positive for the virus, they can voluntarily inform the app and the app will, using the record of proximate interactions, send a notification to the phones it passed in the preceding days.
So, for example, say you strike up a conversation with a friendly shopper in the freezer aisle of your local grocery store and they later learn they have the virus. Assuming you both had Bluetooth toggled ‘on’ and opted to be active on the tracing platform, the infected shopper could report their diagnosis to the app which would in turn push that information to your phone. Armed with knowledge of this exposure you would know to self-quarantine to avoid furthering the chain of transmission.
For a great visual primer on how this would work, see this cartoon – https://ncase.me/contact-tracing/
Reasons to be Optimistic
First, it is positive that organizations who boast massive resources are dedicating money, time and talent to developing tools that may help humanity overcome this pandemic. Like other global challenges we as a species face, coordinated efforts and large-scale mobilization are critical to success. 🙏🌍
Next, from the few details we know at this point, the proposed cooperation and platform rollout are being designed with privacy in mind. Thought of differently, a contact tracing program could be implemented in a variety of ways, many of which pose a significantly greater risk to user privacy than what has so far been announced.
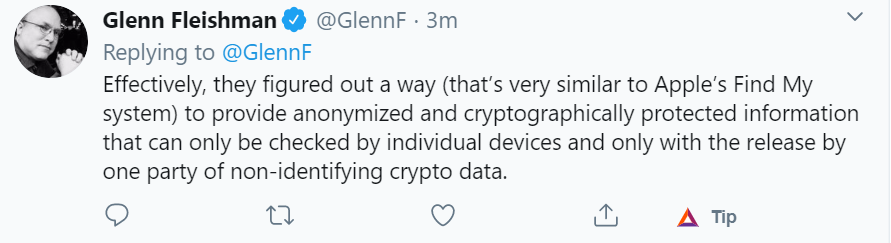
The foremost example of this is the decision to rely on Bluetooth technology, rather than GPS or cell towers, to track a person’s location. Whereas the raw data produced by apps that employ these alternatives often involves storing personal information on a centralized server, in this case, the frequent exchange of Bluetooth pings generates nothing more than a random code (a ‘key’) that is, on its own, meaningless. Further, the only information stored centrally is the database of shared keys and not the interactions between the keys, themselves. The ultimate result is that neither one’s location, nor identity, can be exposed.
Next, the app will be opt-in and so users who test positive for COVID-19 must choose to inform the app that they have been infected. Given that some tech giants have a sticky history of adjusting default settings to maximize data capture without explicit and informed user consent, Apple and Google’s use of the opt-in, rather than opt-out, feature is promising.
Reasons to be Concerned
South Korea, Taiwan and Singapore have, in recent weeks, managed to flatten and bend their infection curves. This achievement has been attributed, in part, to their implementation of aggressive tech-enabled contact tracing programs and has sparked a welcome debate, here at home, about the preservation of civil liberties when Canadians are confronted by a public health emergency.
The greatest sources for alarm focus, rightly, on contact tracing’s intrusion into individuals’ privacy. South Korea’s program, for example, has been naming and shaming infected citizens by publicizing intimate personal information such as their age, gender and credit card information, as well as minute-by-minute log of their movements. Programs in Taiwan and Singapore are less brazen, but only moderately so.
Also, beyond privacy, it is fair to be skeptical as to how effective the technologies will be in achieving their stated aims. For example, what if people simply leave their phone at home? What if only a handful of people decide to use the apps?
Let’s explore some concerns with Apple and Google’s plans specifically.
Private Actors in Public Health. Speaking generally, Apple and Google, even in instances such as this where they are taking pains to preserve user privacy, have every incentive to collect and use the data collected for their own commercial purposes. In fact, doing so is imperative to their business model, especially in Google’s case. The meteoric rise of the so-called tech giants over the past two decades, again, Google in particular, has been made possible through the continual accumulation of user data and its mining thereof to extract behavioural insights to sell to advertisers. Distilled to its crudest form, user data = profit. For now, Apple and Google seem content to build tools to help beat back humanity’s latest existential threat without simultaneously capitalizing on the insights available for capture from this trove of behavioural treasure. But, the sirens sing and in time it may ultimately prove too tempting for either to ignore.
Anonymous Data. Although the data collected in the format proposed would be anonymous, discerning personal information from similar such data is notoriously easy.
Data Sensitivity. Using contact tracing to manage localized outbreaks of a virus means handling people’s health data. The sensitivity of data, like most things, sits on a spectrum. At one extreme lies relatively trivial information such as the most common colour in your wardrobe or the brand of kibbles you buy your puppy. At the opposite end sits data related to your personal health such as blood pressure, family history, genetic information and whether you’ve recently contracted a virus.
Protecting health data is important. In the hands of a healthcare professional, it informs decisions that usually benefit an individual’s well-being. However, in the hands of a less well-aligned actor, say an insurance company or a government, this data may be weaponized against an individual’s interests.
For more on how the broad collection of health data threatens individuals’ autonomy, and therefore, democracy, see this piece by “Sapiens” author Noah Yuval Harari – https://www.ft.com/content/19d90308-6858-11ea-a3c9-1fe6fedcca75.
Shortcomings of the Technology. A drawback of employing Bluetooth technology as proposed is its tendency to create false positives. In the current scenario, this could mean that a person might receive a message informing them they have been exposed to an infected person when in fact they haven’t.
How might this work? The technology doesn’t account for walls and so if you are at home in your apartment your phone may log interaction with your neighbour in the suite below. If that same neighbour happens to one day report an infection using the platform, you may be alerted to a possible exposure despite the fact that you haven’t actually come in close contact.
Additionally, the technology doesn’t account for the duration of a potential exposure. It goes without saying that if you spend a day working beside someone you will have a greater risk of transmission than if you happen to linger near them momentarily in the frozen food aisle.
There are several security risks as well, but for the moment, those are beyond my comprehension. For those interested, this Twitter thread offers some early analysis on possible security flaws.
Maintaining Accountability (Overseeing The Saviours)
Crucially, several measures can, and ought, to be taken to ensure that Apple and Google’s initiative helps address the present crisis and does not devolve into an unauthorized data grab.
- Monitor changes to the terms of service policies and user agreements. Even though few users read them, they nonetheless govern the relationship between users of technology and its creators. How is data being collected? For what purposes is it being used? Who is granted access? What controls are in place?
- Delete unnecessary data. Not all moments are usefully traced.
- Avoid mission creep. Although we are currently in crisis, we remember that this too shall pass. Accordingly, we must ensure that any extraordinary powers or permissions granted to fight the virus don’t, once the situation is under control, continue. Think PATRIOT Act in the wake of 9/11.
- Keep code open and allow for external audits thereof.
Conclusion and Further Reading
Rare moments when adversaries find common ground to spur the common good are causes for celebration. As COVID-19 wreaks havoc on humanity, all ideas should be on the table and most offers of help should be welcomed. But, as their proposed program is further designed and then deployed, we must help Apple and Google focus their efforts on helping beat the coronavirus, and nothing more. Once we emerge from this dark period, we mustn’t have allowed them to have charmed us with their unity. After all, friends can, on different days, be enemies.
The links below offer additional insights into topics related to this theme:
- ACLU white paper – https://www.aclu.org/report/aclu-white-paper-limits-location-tracking-epidemic?redirect=aclu-white-paper-limits-location-tracking-epidemic
- White paper on DP3T, the technological system which underpins G&A’s proposal – https://github.com/DP-3T/documents/blob/master/DP3T%20White%20Paper.pdf
- Draft technical documentation from the G&A partnership – https://www.apple.com/covid19/contacttracing/
- Thoughtful submissions to US Senate regarding the proposal – https://www.commerce.senate.gov/services/files/D069F0C0-2B67-4999-AC75-5BC41D14D00C
- CCLA post – https://ccla.org/blog-2/

